[ad_1]
Adopting and leveraging a holistic strategy just like the NIST Cybersecurity Framework is a brilliant thought—defending your group from cyber threats is important. Listed below are some key concerns you might have considered trying to remember, and the way HPE Training Companies may also help.

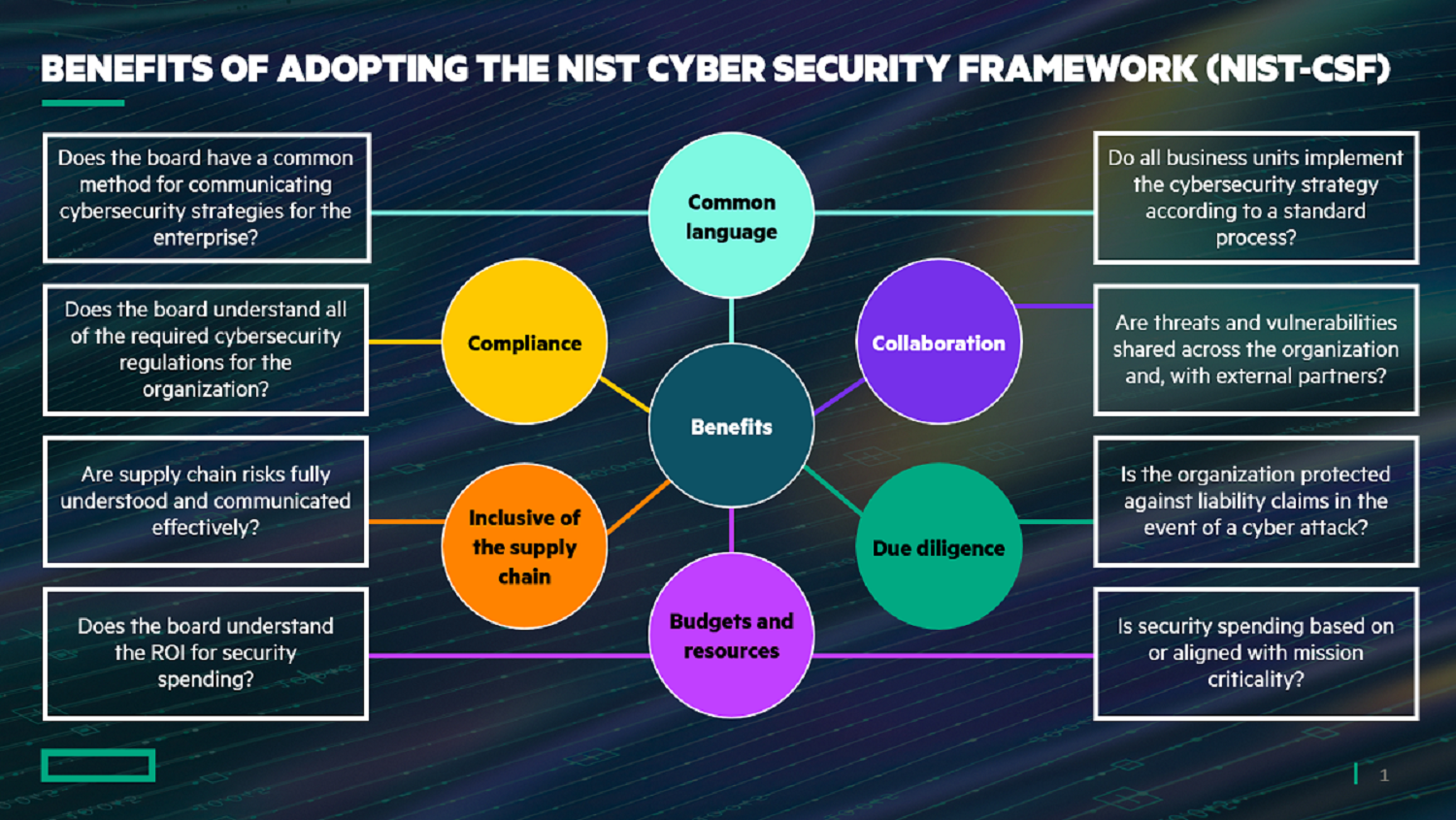
Organizations make use of quite a few cyber safety danger administration capabilities—however with out an overarching cyber danger framework, they fall in need of implementing a holistic strategy which serves to “pull all of it collectively.” Though there are a lot of frameworks at your disposal, the NIST Cybersecurity Framework (NIST-CSF) is very helpful to assist coordinate completely different focus areas, carry out hole evaluation, and determine and prioritize areas of enchancment.
The next greatest practices will assist your group successfully implement a sturdy cybersecurity danger administration framework.
Supply: HPE NIST Cybersecurity Skilled (NCSP) Certification Coaching
1. Align all ranges of your group – starting on the high
The first goal of adopting a framework just like the NIST Cybersecurity Framework needs to be to facilitate significant conversations amongst all stakeholders throughout your group—this could embrace the board of administrators, govt management, and senior administration, in addition to the road of enterprise groups and different stakeholders with a vested curiosity. This ensures that the suitable ranges of visibility and consciousness are consulted because the group makes knowledgeable choices about cyber danger investments and commitments.
The choice to undertake the framework should lengthen past IT stakeholders to incorporate members of the board or senior enterprise administration degree executives; additionally they must assist and talk the significance of adopting a cyber danger framework.
It’s also important that almost all (if not all) of your IT division and enterprise liaison personnel have an understanding of cybersecurity danger administration and the steps your group is taking to deal with this. Why? Just because when individuals perceive the goals and objectives of others within the group, you usually tend to get their buy-in and assist, even when they don’t seem to be immediately concerned. Additionally, whereas they might not like having to comply with a safety management, they now perceive why, and so they notice the worth it delivers to the group.
HPE’s coaching and certification program begins with a Basis certification that facilitates this requirement – extra on that in a second.
2. Use NIST-CSF Core Capabilities
The NIST-CSF acts as a complete set of steps that your group can take to make sure that cyber danger is assessed. It makes use of purposeful and simple greatest practices, defined with easy-to-interpret enterprise language, to stipulate the Core Capabilities of your group’s distinctive cybersecurity danger administration framework.
Core Capabilities tackle the next:
How will we determine what requires safety?
– What’s its worth to the group?
What safety is required to mitigate the danger?
What ranges of resilience needs to be constructed within the face of those cyber threats?
How shortly can we detect that our protections have failed?
How shortly can we reply to restrict or keep away from injury?
How shortly can we totally get well?
Core Capabilities dramatically enhance senior management’s understanding of the strategic outcomes and interdependencies throughout your enterprise. Through the use of Core Capabilities, you’ll be able to facilitate discussions about completely different units of cyber danger controls, higher perceive your group’s cyber danger profile, and guarantee that you’ve got a ample stability of controls.
3. Construct consciousness
It is very important assess controls, determine and execute enhancements, and reply to adjustments in vulnerabilities, threats, dangers, and asset worth. Whereas finishing up this work, your group may nonetheless expertise a cyber incident at any time, so that you must be ready. A sturdy playbook of responses or insurance policies to deal with the almost definitely kinds of cyber incidents, together with remedial actions, is required.
pre-cursor or parallel exercise is to implement an efficient consciousness program. This not solely demonstrates dedication to cybersecurity protection throughout your group, nevertheless it additionally offers a degree of improved safety all through your journey.
By bettering safety consciousness, workers are empowered to maneuver from being a supply of vulnerability to turning into the primary line of protection (what I wish to name “human firewalls”). A security-aware workforce can turn into an asset and is a vital constructing block of your cyber protection. Be taught extra in my earlier put up: Cyber Safety Consciousness: Learn how to Set up an Efficient Program.
4. Perceive, assess, and prioritize
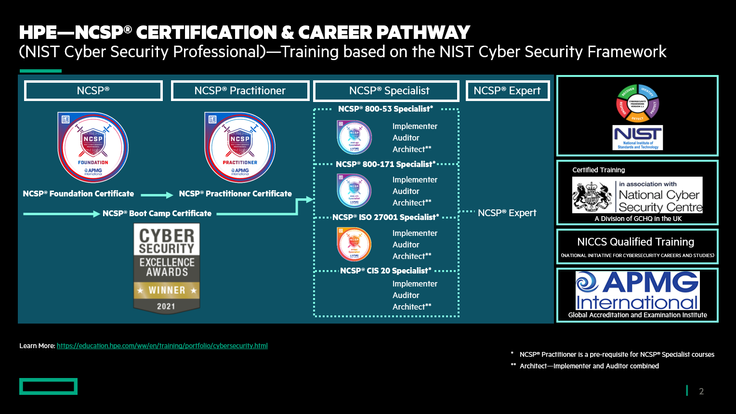
The NCSP® (NIST Cybersecurity Skilled) certification program is designed to supply the data, expertise, and functionality your group must construct a roadmap on your cybersecurity journey. That is just like what ITIL® does for service administration: ITIL offers a typical structured understanding and strategy to a corporation’s working mannequin.
Step one for the cybersecurity workforce is to grasp your group’s wants and desired outcomes. Then, the workforce should assess numerous dangers and take into account the controls wanted to mitigate these dangers, whereas on the similar time evaluating the impression of the controls on the group’s capacity to realize desired outcomes. Lastly, the workforce must set out a program of enhancements that prioritizes actions recognized as most necessary to the group, similar to defending income streams or decreasing the danger to progress initiatives.
This can be a lot of labor and shouldn’t be underestimated by way of data, expertise, talents, time, and sources required. Having an accredited, workable plan is crucial to your success
5. Be agile, unconstrained, and progressive
Cyber danger is a continually transferring and evolving goal. Because of this all vulnerabilities, threats, and menace actors will change, as will the belongings that your group wants to guard.
It’s important that your group doesn’t look upon cybersecurity as a ‘one-time challenge’ with ‘one-time funding.’ It must be inherently a part of your online business technique.
Your cybersecurity technique should be an ongoing precedence, with continuous enchancment and innovation to make sure that the scope and mitigation of danger evolves to satisfy the altering threats to your group. (‘Plan, Do, Test, Act’ is a well known course of to comply with.
6. Undertake and adapt
Adopting and adapting the framework to fit your group are keys to your success. Take into account that frameworks are steerage—not the regulation. Greatest practices just like the NIST-CSF and ITIL® are confirmed to work for a lot of organizations; nevertheless, they aren’t “silver bullets” or panaceas—so fixed scrutiny and evaluation is required to resolve what works greatest on your group now and sooner or later.
7. Create aggressive benefit
A sturdy and pragmatic cybersecurity danger administration program offers a chance to realize aggressive benefit.
For instance, a corporation that has, or is a part of, a provide chain that decides to undertake the Cyber Provide Chain Danger Administration (C-SCRM) safety controls, could be independently audited utilizing the Cybersecurity Maturity Mannequin Certification (CMMC). This certification offers a degree of consolation to prospects and fellow suppliers, producing a aggressive edge and, finally, extra enterprise.
That is just like what we see with the elevated adoption of Zero Belief. Not solely do organizations acquire a larger degree of safety for themselves and their prospects, they obtain a “badge of dedication,” seen to everybody, that they will use to advertise and market themselves.
8. Leverage HPE Training Companies coaching and certification assist.
HPE gives NIST Cybersecurity Skilled (NCSP®) Certification coaching and examination preparation in a wide range of supply codecs—eLearning, conventional classroom-based coaching, and digital instructor-led coaching (VILT).
Be taught extra concerning the award-wining NCSP certification programs from HPE:
Supplies a typical language and a elementary understanding of cybersecurity danger administration and the NIST-CSF.
Learn how to strategy, design and construct a complete cybersecurity and danger administration program based mostly on the NIST-CSF.
Basis and Practitioner mixed.
Moreover, NCSP Specialist Programs are anticipated to be launched in October 2021.
Reinforce your cyber-resilience with HPE
HPE has industry-recognized experience in safety, danger and compliance companies (a part of HPE Advisory and Skilled Companies). We have now distinctive experience on the subject of aiding organizations with defending or recovering from cyber threats and assaults.
Be taught extra about HPE Advisory and Skilled Companies designed to enhance cyber-resilience:
- HPE GreenLake Cloud Companies – Safety Danger and Compliance Observe
- HPE Advisory and Skilled Companies safety consulting
- HPE Server Safety and Infrastructure Safety Options
- Cybersecurity Coaching from HPE Training Companies
Or contact HPE to begin a dialog.
Prepare for October Cybersecurity Month
As a thank-you for studying this weblog and to have fun the annual “October Cybersecurity Month,” please click on this hyperlink to win a free copy of our one-hour eLearning, NCSP Consciousness.
John F McDermott manages the HPE worldwide portfolio for cybersecurity training, coaching and certification. For the previous 5 years, he has introduced his 35+ years’ expertise in IT Service Administration greatest practices to the cybersecurity world.
Contact John on Linkedin and on Twitter.
Companies Consultants
Hewlett Packard Enterprise
twitter.com/HPE_Pointnext
linkedin.com/showcase/hpe-pointnext-services/
hpe.com/pointnext
[ad_2]