[ad_1]
Traditionally, software program safety has been addressed on the mission degree, emphasizing code scanning, penetration testing, and reactive approaches for incident response. Lately, nevertheless, the dialogue has shifted to this system degree to align safety with enterprise targets. The perfect end result of such a shift is one wherein software program improvement groups act in alignment with enterprise objectives, organizational threat, and answer architectures, and these groups perceive that safety practices are integral to enterprise success. DevSecOps, which builds on DevOps ideas and locations further concentrate on safety actions all through all phases of the software program improvement lifecycle (SDLC), will help organizations understand this ideally suited state. Nevertheless, the shift from project- to program-level pondering raises quite a few challenges. In our expertise, we’ve noticed 5 widespread challenges to implementing DevSecOps. This SEI Weblog put up articulates these challenges and offers actions organizations can take to beat them.
Key Advantages of DevSecOps
The addition of safety to the observe means addressing safety all through the lifecycle, from the idea of a function to the deployment of a product. The necessity for widespread ideas and practices that span the group can itself current a problem. Along with ideas and practices that span the group and govern the lifecycle from idea to deployment, DevSecOps requires the next practices:
- iterative and incremental improvement—This observe includes a cyclical method to breaking software program improvement into smaller, extra manageable steps. Steady integration/steady deployment (CI/CD) practices present the automation crucial to make sure high quality, safety, and performance.
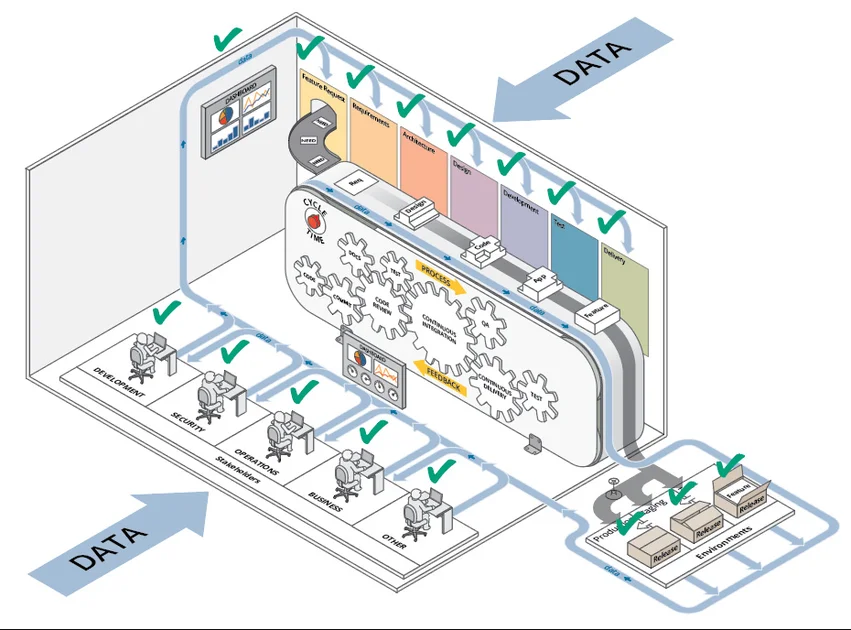
- steady suggestions—Suggestions must be collected all through each step of the lifecycle to permit for skilled validation and basic observability. Each instrument used all through a DevSecOps pipeline creates some output that can be utilized for suggestions. Take a look at circumstances produce output that gives high quality suggestions, stakeholders and prospects provide a supply of human suggestions. Determine 1 illustrates the sorts of knowledge, and their sources, that may inform the suggestions and measurement cycle.
- metrics and measurement—Metrics are used to judge suggestions and decide how properly the group is acting on measures, equivalent to productiveness and high quality.
- automation in each part of the Software program Improvement Lifecycle (SDLC)—Automation helps organizations benefit from their suggestions mechanisms. CI/CD is the first automation mechanism of the SDLC.
- full engagement with all stakeholders—All stakeholders have to be engaged, not simply the Dev, Sec, and Ops elements. This engagement ought to produce consensus on what issues probably the most to the group.
- transparency and traceability throughout the lifecycle—Transparency helps construct the belief wanted among the many Dev, Sec, and Ops groups to make the method work, and traceability allows the digital path of the merchandise used to construct, deploy, and keep software program.
These practices produce a number of advantages when utilized in DevSecOps. Maybe the 2 most necessary are the next:
- diminished safety error and related prices—By addressing safety points all through the event lifecycle reasonably than after launch, organizations can catch and tackle points earlier, when the time and price to resolve them is way decrease. These prices embrace misplaced {dollars}, further effort and rework, and buyer goodwill.
- diminished time to deploy—Catching flaws and vulnerabilities via fixed testing in the course of the lifecycle reduces time to deploy, reduces time spent after deployment on error response, and improves your readiness to deploy.
Along with fewer errors and vulnerabilities, diminished prices, and diminished time to market, DevSecOps additionally offers the next advantages:
- repeatable and/or automated steps
- steady availability of pipeline
and software - elevated time for studying new ideas
- responsiveness to enterprise wants
- elevated stability and high quality
DevSecOps Challenges
Whereas DevSecOps can profit your group in some ways, we’ve noticed a number of challenges to its adoption, the most typical of that are the next:
- lack of safety assurance on the enterprise and mission ranges
- organizational limitations associated to collaboration, tooling, and tradition
- impression to high quality as a result of safety isn’t a precedence whereas methods are getting extra advanced
- lack of safety abilities for builders, enterprise stakeholders, and auditors
- inadequate safety steerage as a result of lack of assets, requirements, and knowledge
The remainder of this part examines every of those challenges and offers approaches for overcoming them.
CHALLENGE #1: Lack of Safety Assurance
How do we all know that the safety practices we’ve adopted for our improvement lifecycle and constructed into our software program are sufficient and acceptable for the enterprise goal we’re attempting to deal with? Addressing this problem will be exhausting, particularly when your business, enterprise, and/or mission lacks safety assurance.
Your Trade Lacks Safety Assurance Fashions
The safety necessities in your business or area are totally different from these of different industries or domains. As an example, the well being care business has totally different safety necessities from the monetary sector. In case your business lacks assurance fashions, you would possibly start by assessing your individual group’s safety posture and necessities, then have interaction with comparable organizations in your business or area to share data. As well as, we advocate the next:
- Don’t watch for an business commonplace to emerge.
- Be a part of or create casual working teams with business friends.
- Attend conferences and community with like organizations.
- Share your experiences and classes realized.
- Work with others to increase the physique of data and set up greatest practices.
Your Enterprise Lacks Safety Assurance
There’s usually a disconnect between enterprise wants, mission, and imaginative and prescient on the subject of safety. Builders want to know the enterprise context of safety. They need to take into consideration the group’s safety insurance policies, its enterprise drivers, and the way these apply to the software program being developed. In so doing, they need to tackle safety as early as potential within the lifecycle, ideally in the course of the necessities stage. As you do, hold the next suggestions in thoughts:
- Give attention to fundamentals: What are the threats? What are the enterprise drivers? Steadiness the 2.
- Align with improvement with enterprise wants (time to market, value financial savings, resilience).
- Conduct exterior audits.
- Perceive the enterprise context.
- Establish, hyperlink, and rank enterprise and technical dangers.
- Establish safety necessities in early.
- Outline the danger mitigation technique.
- Educate prime administration and get them onboard.
- Have interaction extra senior technical folks first to work with safety groups.
- Make safety a part of senior technical opinions; organically unfold the phrase.
Your Mission Lacks Assurance of Safety
When you’ve recognized safety assurance wants inside your business or area (and maybe your particular enterprise inside that area), it’s essential map that knowledge to your mission. As an example, maybe your group is already following steerage, equivalent to Normal Information Safety Regulation (GDPR) or the Well being Insurance coverage Portability and Accountability Act (HIPAA). You might want to account for any safety actions stipulated in that steerage in your mission planning, and also you want to take action early within the lifecycle when there’s nonetheless time to deal with it. As you do, bear in mind the next suggestions:
- Map reporting knowledge from instruments to kind a steady view of worth.
- Run safety instruments on all code to measure code high quality and requirements.
- Overview code modifications for safety and doc approval previous to launch.
- Use devoted testing assets within the case of serious modifications.
- Monitor all modifications and approvals for incident functions.
- Conduct code opinions.
- Expose safety crew to your metrics and knowledge.
CHALLENGE #2: Organizational Limitations
For those who’re not sharing your DevSecOps journey throughout the group, from idea to product, it’s best to anticipate issues because you gained’t have a transparent understanding of the enterprise wants your software program wants to deal with. You won’t actually have a clear imaginative and prescient of the client’s wants and the atmosphere wherein the client operates. Communication is essential to breaking down organizational limitations, however usually totally different items inside a corporation use totally different communications instruments, buildings, and objectives.
To start to interrupt down these limitations, briefly doc your journey from thought to product. Have a look at factors of interplay among the many varied elements of your group. Educate executives who seemingly don’t know the small print of the DevSecOps course of. Construct connections and a tradition that reinforce the sharing of the identical objectives and imaginative and prescient. Usually, poor stakeholder collaboration, problem integrating pipeline safety, and an unwillingness to make safety a precedence stand in the best way of profitable DevSecOps implementation.
Poor Stakeholder Collaboration
The product you’re creating touches many different stakeholders in your group, together with advertising and marketing, IT, and authorized groups, however communication amongst them is likely to be missing. For instance, you might have totally different instruments, might not share the identical infrastructures, and will not even share the identical imaginative and prescient and objectives. To deal with these points, it’s essential come collectively and doc your journey from idea to product. A easy cheat sheet will suffice, one which reminds all stakeholders of the imaginative and prescient, the mission, and the roles they are going to play within the lifecycle. Our suggestions for enhancing stakeholder collaboration embrace the next:
- Doc your present state and establish silos (e.g., improvement, infrastructure, and safety).
- Begin constructing collaboration between the Safety, Dev, and Ops groups.
- Be ready: folks typically don’t wish to change their tradition and/or workflow.
- Ensure everybody will get on the identical web page relating to the significance of safety (from executives to DevSecOps groups).
- Instill a steady safety mindset.
- Give attention to partnership, not unhealthy battle. Destroy the blame tradition.
- Get stakeholders to agree on a shared a imaginative and prescient for the mission.
- Steadiness workload amongst groups concerned.
- Put safety folks into improvement groups.
Integrating Pipeline Safety
The pipeline isn’t solely the infrastructure supporting DevSecOps. As a substitute, it’s the heartbeat of your complete DevSecOps ecosystem, together with supply management, communications, problem monitoring methods, documentation methods, CI/CD, and code evaluation. This infrastructure must be linked, i.e., all of the instruments ought to talk to one another, as proven in Determine 2.
As an example, your supply management ought to be capable of talk together with your construct server, your communication methods, and your problem monitoring methods. When your infrastructure is linked this fashion, you may apply menace modeling, static evaluation, dynamic evaluation, mission administration, or interactive software safety evaluation. Take into consideration instrument integrations to beat pipeline safety issues after which design your infrastructure to deal with safety.
The pipeline is the place transparency occurs and the place all of the stakeholders implement their experience through automation. One approach to obtain this transparency is thru metrics dashboards fed by pipeline knowledge which might be straightforward to learn. The instrument must be tailor-made to the product. The larger you’re, the more durable that is to do, however the result’s price it. Suggestions for integrating pipeline safety embrace the next:
- Combine your course of with menace modeling (TM), static software safety testing (SAST), dynamic software safety testing (DAST), and interactive software safety testing (IAST).
- Set up safety necessities traceability.
- Apply metrics: imply time to restore (MTTR), imply time to detect (MTTD), vulnerability escape fee, repeated incident root trigger, time to deploy the app from improvement to manufacturing.
- Have a look at totally different approaches: abuse circumstances, architectural threat evaluation, software penetration testing.
- Design for safety.
- fail securely and fail protected defaults
- least privilege
- protection in depth
- Automate the place potential.
- infrastructure as code (IaC), virtualization, containers, and cargo balancing
- configuration administration
- steady software and efficiency monitoring
Making Safety a Precedence
You might want to plan for safety if you wish to make it a precedence. Deal with safety as a function that your software program will need to have. In some circumstances, the selection is out of your palms: a software program invoice of supplies (SBOM), as an illustration, would possibly mandate constructing safety into the product. However how do you make safety a precedence? We advocate the next:
- Use evangelists to drive tradition change.
- Clarify why safety is a vital, shared duty, and its impression.
- Embed safety into operations escalation.
- Invite the safety crew to postmortems.
- Create a plan in small components; begin with a pilot and be conscious of cross-team useful resource constraints.
- Hold it easy; don’t overwhelm the system. If there are too many issues to do, the plan is more likely to fail.
- Incrementally chase actual threat and threats first.
- Take a look at whether or not your group is prepared for the tradition change; no single know-how/instrument will get you DevSecOps.
CHALLENGE #3: Lack of High quality
Safety is integral to high quality. In our remark, lack of high quality is commonly related to the safety crew getting concerned too late, a insecurity within the launch, and system complexity.
Safety Staff Concerned Too Late
Too usually, builders make safety a secondary precedence, particularly when they’re below stress to maintain manufacturing transferring ahead. As we acknowledged earlier, safety is a key facet of high quality. When the safety crew engages in the direction of the top of the SDLC course of, it’s usually too late to keep away from the disruption and costly rework that flows from the safety flaws it identifies. Relying on the mission cadence, “too late” might imply two months, two weeks, and even two days.
Contemplate a crew utilizing Agile improvement with two-week sprints. Inside that dash, given a scrum day by day, the developer would want to know of any issues as early as potential. Nevertheless, the Sec crew solely analyzes the code a month later (or perhaps two months later or simply earlier than deployment to the manufacturing atmosphere). Any issues found by the Sec crew at this level would require large work, and builders will push again. Furthermore, the later issues are found within the SDLC, the dearer they’re to repair. To keep away from these points, we advocate the next:
- Begin getting safety and compliance necessities in early.
- Tie compliance targets into offering assurance again to the enterprise.
- Take a look at compliance towards safety insurance policies to establish gaps.
- Outline a threat mitigation technique early.
Lack of Confidence within the Launch
Correcting issues and patching safety vulnerabilities late within the improvement lifecycle when the stress is on to get the product out the door opens room for doubt in regards to the high quality of your launch. This insecurity hinders planning and efficient use of assets as it’s essential reserve assets to deal with flaws and vulnerabilities found after launch. These flaws and vulnerabilities characterize a chance value, a greenback value, and a reputational value. However there are methods to enhance confidence in your launch, together with the next:
- Instill risk-based safety testing.
- Transfer the dialog from CABs and part gates to compliance pushed releases.
- Automate reporting for compliance violations and cease the pipeline when the edge is exceeded, or coverage not met.
- Transfer towards frequent, automated audits.
- Audit your self to display compliance with insurance policies or rules.
- Set up safety necessities traceability (a function DevOps offers) and hint every little thing: code, artifacts, pipeline, take a look at circumstances, and many others.
System Complexity
Contemplate a fancy system with a number of software programming interfaces (APIs) and microservices. How do you gauge its high quality? How have you learnt that every of the providers is following the appropriate safety controls? How have you learnt that every API is following centralized communications? How have you learnt that they’re following the safety insurance policies that you just implement in organizations? You might want to incorporate these insurance policies in your code, in your architectures, in your microservices. To take action, it’s essential accumulate the appropriate knowledge and metrics that allow you to look at all of the elements all through your advanced system. The extra advanced your system, the extra you want a testing atmosphere that mirrors your manufacturing atmosphere. Briefly, we propose the next:
- Establish proxy metrics for complexity, such because the variety of points in manufacturing and the time to deploy an software.
- Drive safety insurance policies into manufacturing by integrating safety duties in early levels of the DevSecOps pipeline.
CHALLENGE #4: Lack of Safety Abilities
Builders, architects, scrum masters, and different key gamers in a corporation ought to have the appropriate vocabularies and abilities. By vocabularies, we imply some widespread data or skillset, or a standard understanding, equivalent to a data of methods to write safe code. In our expertise, this lack of a standard vocabulary usually manifests in 3 ways: The enterprise lacks safety abilities, builders lack safety abilities, and/or auditors lack safety abilities.
The Enterprise Lacks Safety Abilities
Enterprise stakeholders want to make use of the vocabulary of safety. In fact, not everybody will be an skilled at every little thing, however the enterprise stakeholders ought to be capable of perceive and articulate safety necessities and join these safety necessities to organizational dangers. An acquisition crew, as an illustration, ought to be capable of realize it’s buying the appropriate safety practices when it’s buying a product. To enhance on this space, we advocate the next:
- Shift the dialog to threat and high quality.
- Service and shield the enterprise pursuits to decrease threat (establish threat and/or safety worth).
- Establish architectural threat and uncertainty and map these dangers to compliance, resiliency, and have supply.
Builders Lack Safety Abilities
We prefer to assume that builders know every little thing wanted to carry out their duties efficiently. Builders actually know methods to write code, however they’re usually not skilled for safe coding in particular languages on the college degree or in abilities improvement packages, the place the main focus stays on function improvement. It takes time to be taught these abilities, and to observe utilizing them, nevertheless it’s worthwhile for the group to develop these safety abilities amongst its workers, to develop. This upskilling can take the type of safety coaching or different packages and assets that incentivize and inspire improvement workers to accumulate and develop these abilities.
You can begin small with a slender focus. As an example, ask your self, “What are the highest 10 vulnerabilities we’ve got addressed in our organizations? What are the highest 10 CVEs? What are the highest 10 CWEs?” Give attention to coaching that addresses these points and widen your scope over time. Or begin with the programming language(s) utilized by your group and focus safety coaching on these languages. Different suggestions for constructing safety know-how amongst your improvement workers embrace the next:
- Hold the endgame in thoughts and construct a collaborative safety tradition.
- Implement compliance automation to drive enterprise pondering into the SDLC.
- Don’t make safety coaching a checkbox. Safety coaching every year has restricted effectiveness.
- Intention for angle and habits: Merely offering higher technical coaching alone gained’t change attitudes.
- Encourage and unblock the trail to your purpose: Take away job ambiguity, set clear position targets, and don’t overload.
- Intention for long-term retention and apply studying in context repeatedly.
- Rotate safety specialists on the crew, the place potential.
Auditors Lack Safety Abilities
Auditors evaluation code and merchandise, rendering a thumbs-up or a thumbs-down based mostly on established standards, however they often don’t have the talents and data to offer an correct judgment about safety. To compensate, foster robust relationships amongst auditors and builders. Educate auditors in your structure and methods. As we famous earlier within the part on enterprise stakeholders, make sure that your auditors perceive and use the identical vocabularies. Different suggestions embrace the next:
- Construct working relationships and collaboration throughout silos.
- Make safety part of casual discussions.
- Present cross-functional coaching for each technical and compliance domains.
- Combine low-disruption workflows.
- Get acquainted with some widespread requirements and frameworks (OWASP Prime 10, NIST 800-53, and ISO 27001).
CHALLENGE #5: Inadequate Safety Steering
Organizations must take inventory of their compliance practices and safety insurance policies and implement them of their merchandise or capabilities. As an example, you might have adopted zero belief insurance policies, however how will you implement them? Contemplate the place your group is in its DevSecOps journey and map out your future: What are you doing for yr one? 12 months two? Past? Bear in mind, if you wish to create a brand new commonplace in your group, you would possibly assume you’re distinctive, however you’re not. As a substitute of ranging from scratch, use an current commonplace or attempt to tailor one to your wants. As an example, you would possibly begin with the OWASP Prime 10. How will you implement these frameworks in steerage below CI practices? Incorporate the insurance policies into the workflow from starting to finish.
In our expertise, issues on this space stem from three deficiencies: lack of safety assets, lack of safety requirements, and/or lack of proactive monitoring.
Lack of Safety Assets
You most likely don’t have sufficient safety folks on the crew, but there are insurance policies and steerage to develop. Furthermore, there’s a lot else that should occur. For those who’re fortunate, you may need some unicorns in your crew, some overachievers, however it’s essential get past that. Listed below are some suggestions for organizations that wish to embark on a DevSecOps journey however lack safety assets:
- Begin small by introducing a coverage and assess your gaps. Develop from there.
- Map insurance policies to domain-specific procedures (e.g., improvement and testing) and implement in product (e.g., zero belief).
- Intention for long-term sustainability: If you consider an upgraded functionality a few years after deployment, is the change nonetheless there?
- Unfold safety duty throughout a number of folks.
Lack of Safety Requirements
Right here’s the excellent news: As we’ve famous, a number of safety requirements have already been developed. You don’t have to start out from scratch. You can begin with insurance policies derived from current requirements, tailor them to your wants, and incorporate them into your practices and merchandise. When doing so, hold these suggestions in thoughts:
- Don’t go huge bang. Begin with one thing manageable, equivalent to static evaluation, and develop from there.
- Begin with a widely known framework like OWASP Prime 10 and create just a few insurance policies derived from that.
- Intention at low hanging fruit (CI or testing, for instance) and measure safety towards your preliminary insurance policies.
- Develop by wanting upstream and downstream for the next-easiest implementation.
- Bake insurance policies into the workflow to keep away from regression.
Lack of Proactive Monitoring
Proactive monitoring [DS1] identifies and addresses safety dangers earlier than an assault occurs. The important thing to growing extra proactive monitoring is to have a look at circumstances wherein you’ve been pressured to react, then plan methods to get in entrance of the issue. As an example, you might have found sure vulnerabilities, or courses of vulnerabilities, after previous releases. Take into consideration how one can tackle these sorts of vulnerabilities in your pipeline and develop a observe round that after which incorporate it as early as you may in your SDLC.
There are nice open-source and industrial monitoring instruments out there. Whereas every of those instruments has a person dashboard, ideally pe the outcomes from all of them must be built-in into a standard dashboard. Doing so will present an overarching view into your DevSecOps journey for each the group and your particular person merchandise. We additionally advocate the next:
- Begin with Ops log monitoring earlier than trying costly instruments.
- Create suggestions loop from Ops again to improvement.
- Replace safety documentation, together with belief boundaries, new threats, and element verification.
Conclusion: Sustaining your DevSecOps atmosphere
Implementing DevSecOps will be daunting. Challenges abound. This weblog posting examined the 5 commonest challenges and approaches for overcoming them, however maybe the overarching problem is the scope of the duty. Specifically, you wish to understand the advantages of DevSecOps, however you are worried your group lacks the assets and know-how to realize a completely realized DevSecOps atmosphere. The prospect will be overwhelming, which is why all through this put up we’ve got characterised the method as a journey and really useful beginning with small steps you may handle and construct on. As you achieve this, hold this cyclical course of in thoughts:
- Assess your gaps.
- Establish fast wins.
- Empower champions and spotlight accomplishments.
- Measure outcomes, reassess gaps, and construct on fast wins.
- Consider and repeat.
[ad_2]